Cyber Community
Staying Operational is Essential
Developing a cybersecurity culture within an organization is about diligence in protecting the authority's public safety obligation, information, and environment. Having a regular training programme is essential. The training begins with email and ends with the preservation of life and structures.
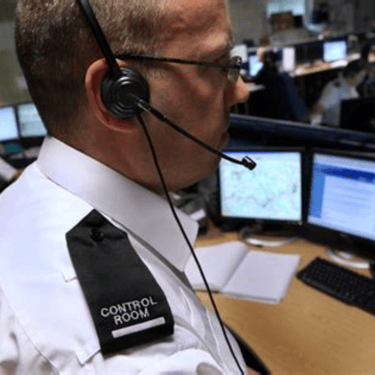
Police and security use IP tools to manage a multitude of security systems within a security environment. These systems must be protected to ensure public safety and critical infrastructure. This requires an integration of team functions between law enforcement and security, those who manage the technical functions of IP. An insider or denial of services is everyone's responsibility. How do we efficiently and effectively provide a secure environment?
Using technology to support law enforcement and security personnel is crucial; it is a mainstay in protecting the environment.
Policies and procedures must be in place to help public safety and security workers ensure technology is usable and beneficial.
What Happens If It's Not?
PLAN!



The cyber community is worldwide and has few actual restrictions or controls regulating activity or the transfer of information. People in the cyber world can remain completely anonymous during communication if they wish to. The lack of restrictions enables great vulnerability to the authorities' critical infrastructure and, at times, public safety.
Police and security often do not think about cyber security as their responsibility but that of the technology department. Although it is their responsibility, it spills over to security in several ways, from communication, cameras, and computers, to name a few. NO! It is a shared responsibility from IT to all personnel, to police and security. Respectively, each has different and shared responsibilities. Once more, depending on the scope of denial of service, it can fall over to the shared critical infrastructure network: police, security, fire, medical, government,military, and industry.
The basics include written procedures for the authority
Regular training for all employees with internal challenges
Tabletop exercises
Enhanced security protocols for the management of security
Notebooks for written reports
Impaired Incident Response
Law enforcement and security leaders must recognize that cyberattacks are not a matter of if, but when. Proactive preparation and regular incident response exercises are essential.
It is critical to establish in advance how your IT partners will respond during an incident. Most organizations lack the in-house expertise to manage a full-scale cyber response. When internal capabilities fall short, external specialists will be required to handle key tasks such as:
Threat detection and triage
Evidence preservation and forensic imaging
Network-based evidence collection
Incident communication and coordination
Engaging these services ahead of time and on an ongoing coordinated basis—ahead of any incident or crisis—is essential to ensure faster response, better outcomes, and lower costs.


Identify levels of preparedness:
Awareness
Information Sharing
Policy and Procedures
Planning
Employee Training - the weakest link
Cyberattacks are inevitable. Law enforcement and security leaders must prepare accordingly.
Advance planning and regular incident response exercises are essential. Most agencies lack the internal capacity to manage a full-scale cyber incident. It’s critical to define how IT partners will respond and to establish external support before a crisis occurs.
Key response functions include:
Threat detection and triage
Evidence preservation and forensic imaging
Network-based evidence collection
Incident communication and coordination